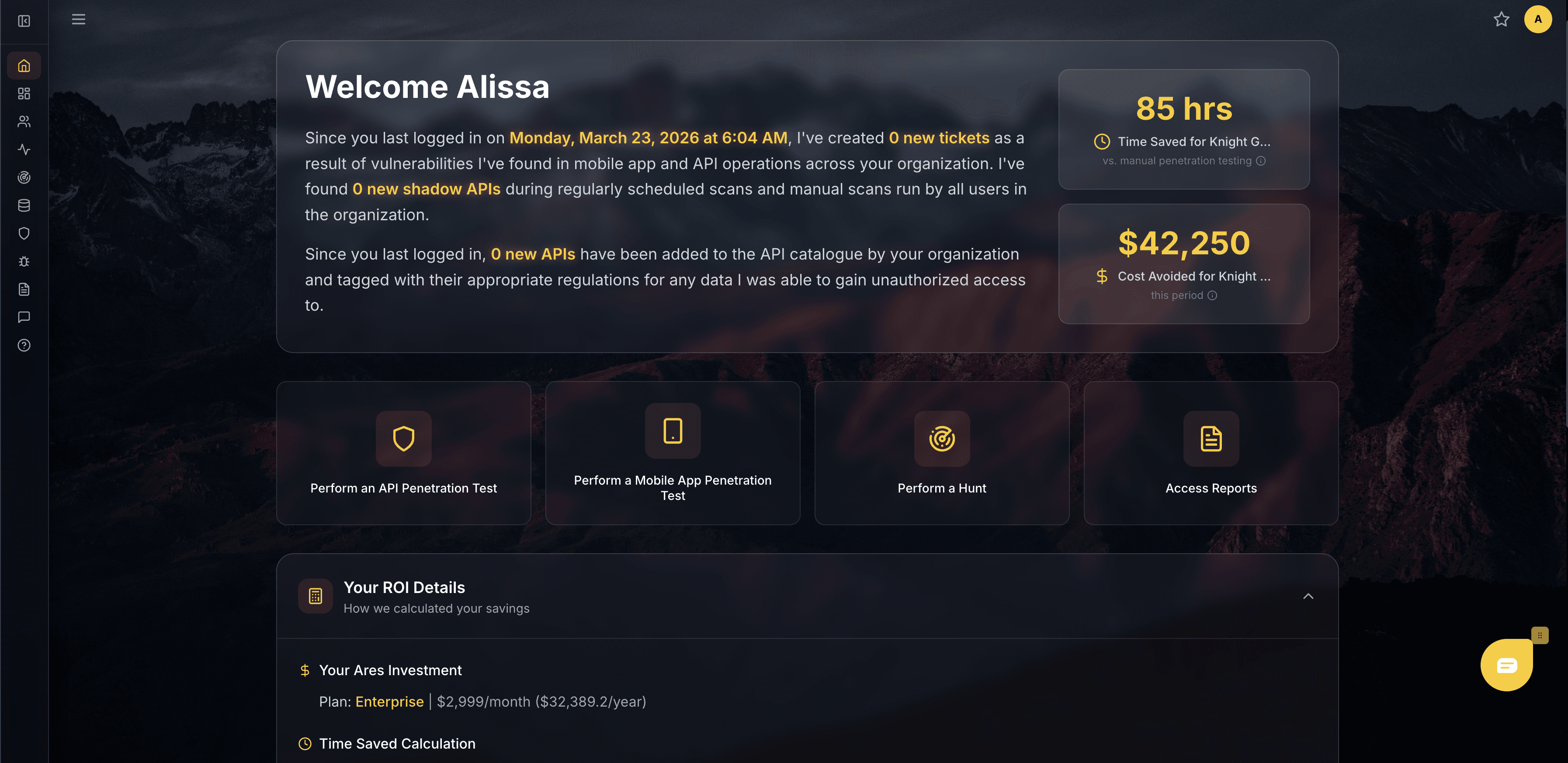
Mapping what you can't see, exploiting what others only flag, and
delivering the evidence that proves your actual risk — continuously and autonomously.
"Assail was founded by Alissa Knight, one of the most recognized API hackers in the world — whose research breaking the APIs of connected cars, financial platforms, and healthcare systems was cited on Capitol Hill and shaped federal cybersecurity policy. After decades of proving what enterprises refuse to see, she built Ares to operationalize that tradecraft — turning decades of offensive expertise into an autonomous platform that hunts and exploits at machine speed."
TESTIMONIALS
Don't Just Take Our Word For It
VERSION 1: DAGGER
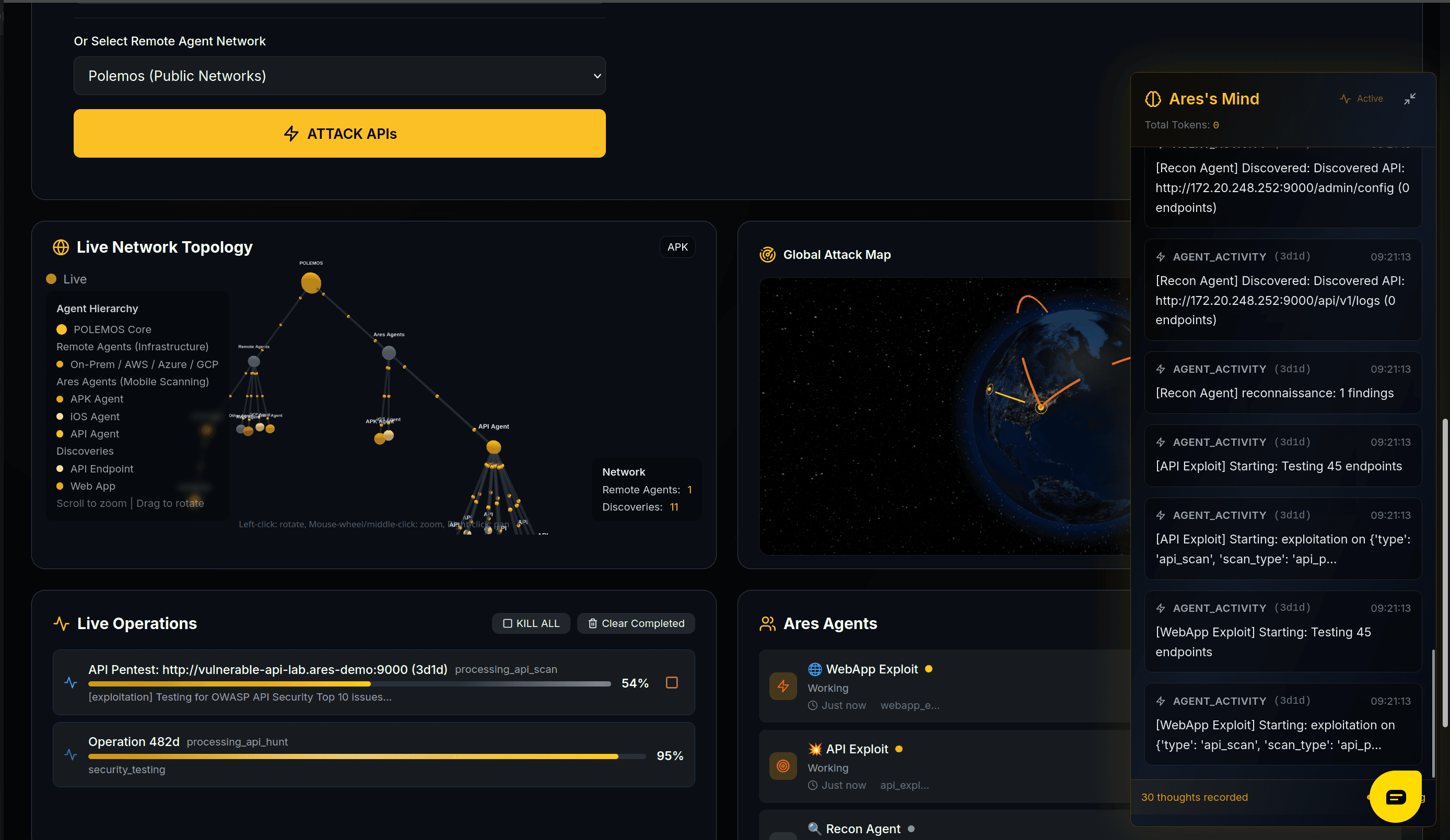
Ares continuously discovers every API across your attack surface, maps the endpoints your team doesn't know exist, and then does what no scanner can — it exploits them. The result isn't a list of theoretical risks. It's validated evidence of exactly how an attacker would breach you, delivered to your team in real time.

BENEFITS
Ares is the world’s first offensive AI platform that continuously hunts, hacks, and secures your mobile and API infrastructure—before the threat actor does.
From detection to exploitation — in one sweep.
Ares completes the mission — discovering, exploiting, and delivering proof of impact.
AI-Driven Growth
Make smarter moves with accurate, real-time business insights.
Attack Surface Visibility
Unvalidated Exposure
BEFORE
AFTER

API Visibility
Ares maps every API across your entire attack surface — including the ones your team doesn't know exist.
FEATURES
All the things you care about and none of what you don't
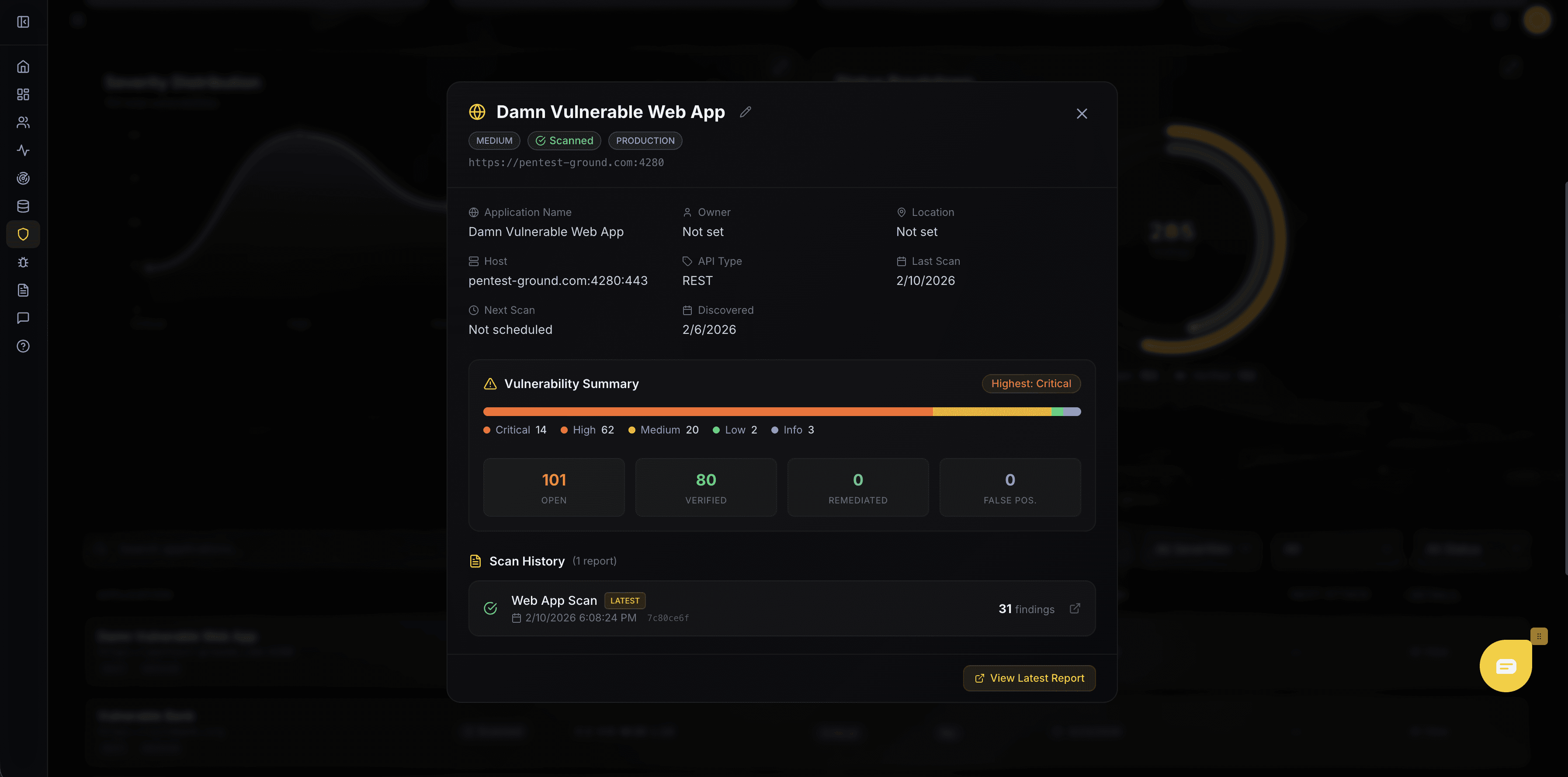
Proof of exploit. Not proof of maybe.
Every finding comes with a full evidence chain — the request Ares sent, the response it got back, and exactly how the vulnerability was exploited. No theoretical risk scores. No flagged possibilities. Your team and your auditors get irrefutable proof that an attacker could breach you, and exactly how they'd do it.
You can't secure what you can't see.
Ares continuously discovers, catalogs, and classifies every API across your organization — including the shadow endpoints your team doesn't know exist. Every API is tagged with compliance mappings, health scores, and attack status so you know exactly what you're exposed to and where to act first.
Leverage AI features that boost performance to your business.
What APIs should I be most concerned about?
Attack the APIs my mobile app is talking to.
What API secrets are hard-coded in my mobile app?
Ask Ares
Talk to Ares
Just like a member of your red team, users can chat with Ares or any of her agents about their environment, how to prioritize remediation efforts, and which vulnerabilities are exploitable. Or just ask how her day was.
One target. Multiple agents. Coordinated assault.
Ares deploys a swarm of specialized agents that share intelligence mid-operation — delivering coordinated red team tradecraft at machine speed. One agent is dedicated to mission planning, which then communicates that plan to the other agents.
CAPABILITIES
Ares autonomously discovers and exploits real vulnerabilities across every layer of your application stack — proving impact through exploitation, not assumptions.
Source: Salt Labs State of API Security Report Q1 2025 — survey of 200+ IT and security professionals